FAIRcon | Measuring DDoS Risk Using FAIR
A step-by-step walkthrough of performing a quantitative risk assessment based on FAIR on DDoS attacks.
Read MoreA step-by-step walkthrough of performing a quantitative risk assessment based on FAIR on DDoS attacks.
Read MoreWord clouds are a great way to visualize text, especially on platforms like Twitter where a great amount of people can be talking about one subject. I recently spent the last 6 days at two San Francisco information security conferences: BSides San Francisco and RSA.
BSides this year was February 28–29 and RSA was February 29-March 4. There’s some overlap in attendees, but the talks and the feeling you get from being at the cons couldn’t be more different. BSides is community driven and the talks are mostly by security practitioners; RSA has a trade-show feel and most talks are conducted by people that work for security vendors.
I was curious about what words showed up most in tweets with the hashtags #BSidesSF and #RSAC and see how different or alike they were. I used the twitteR and wordcloud packages in R to generate these images.
Here’s #BsidesSF:

and here’s #RSAC:
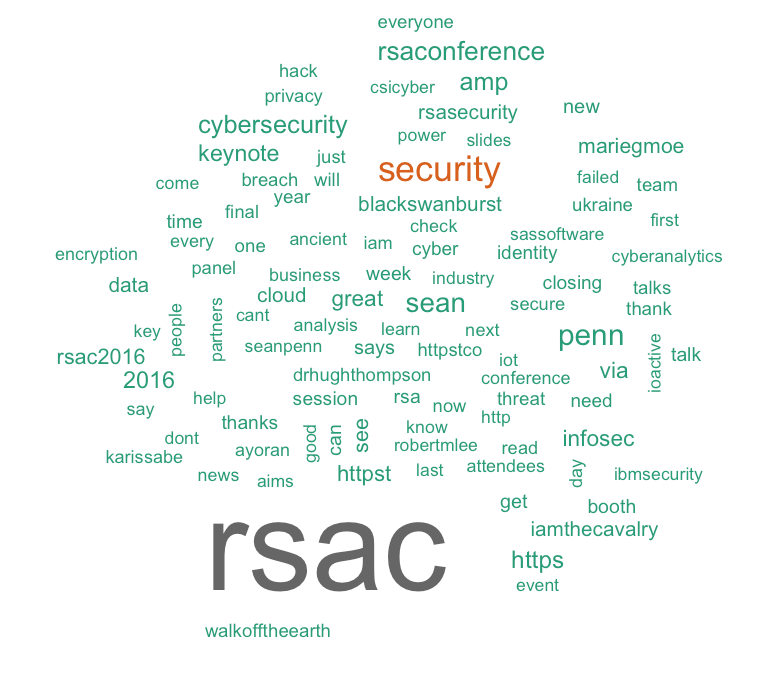
People were definitely tweeting about different things; BSides attendees generally had more positive language and tweeted about presenters. RSA attendees tweeted about keynote speakers (like Sean Penn) and contained a lot of retweets mentions. I am also not surprised the word “booth” was a top keyword in #RSAC, from vendors tweeting out “Come to our booth and get a free pen!”
It was interesting to see the similarities and differences. Let me know what you think.
Ransom is more than just the stuff of Hollywood thrillers. Action packed extortion schemes are as old as history itself, but today’s criminals are trading in information. Extortion rackets such as the Ashley Madison and Sony Pictures Entertainment hacks are well-known cases and many security professionals have experienced ransom attempts of their own, ranging from CryptoWall and CryptoLocker malware to DDoS attacks that promise to continue until the attackers are paid.
Read MoreThe DDoS extortion criminal group, DD4BC, has been hunted ever since the group’s formation in July 2014 by their victims and law enforcement.
One of their first victims, Bitalo Bitcoin Exchange, issued a 100 bitcoin bounty in November 2014 for information on the full and proven identity of the perpetrators. Additionally, an international cooperation of law enforcement has been tracking the group for over a year and a half. DD4BC’s luck finally ran out. On Jan. 12, Europol announced that one person has been arrested and another detained as part of Operation Pleiades, a cooperative investigation that included law enforcement agencies from Austria, Bosnia and Herzegovina, Germany, the UK and Europol.
Read MoreIs using ad blocking software stealing or is it a sound security practice?
On one hand, many websites and content creators make money from advertising. They certainly deserve to be compensated for their time and effort. On the other hand, advertising — at best — can be annoying, and at worst, can serve up malware, suck up bandwidth and redirect confused users to websites without their knowledge.
Read MoreIn May, Lastpass announced an intrusion on its network that led to a data breach of user account information. LastPass is a cloud-based password manager; users load the LastPass extension into their web browsers and all the pesky password management tasks are taken care of. The user is given one-click access to fill in the username and password on known sites and the option to generate a long password and save credentials on new sites.
Read MoreLooking for a great Information Security podcast? There are plenty to choose from! Here’s a roundup of currently active Information Security podcasts.
Read MoreGift cards have caused quite a headache for retailers in the last month, exposing another way that fraudulent activity can eat into razor-thin profit margins. Gift card fraud can range from physical theft to cloning to exploiting programming errors on the merchant side.
The methods of attack are very similar to what is seen with credit card fraud, but gift card fraud is less widely reported in the news. The reason is that, unlike data breaches that involve credit cards, personally identifiable information (PII) is rarely disclosed. Regardless, it is important for both merchants and customers to know how gift card fraud occurs, so they can recognize the behavior and protect themselves.
Read MoreIn 2009, Heartland Payment Systems suffered what was until recently the largest data breach in recorded history, at the hands of a skilled and malevolent hacker. After the attack, the company went on the offensive, implementing numerous protocols to safeguard against a future attack. And hey, lightening doesn’t strike twice, right?
The unfortunate thing about this incident is that Heartland, ever since its 2009 breach, dedicated quite a bit of effort into making sure its name wasn’t in the news again associated with a data breach. The lesson here is, while endeavoring to detect and respond to sophisticated attacks from advanced persistent threats, don’t forget the fundamentals of security.
Read MoreIt’s been a tough few weeks for those of us that are responsible for patching vulnerabilities in the companies we work at. Not only do we have the usual operating system and application patches, we also have patches for VENOM and Logjam to contend with. The two aforementioned vulnerabilities are pretty serious and deserve extra attention. But, where to start and what to do first? Whether you have hundreds or thousands or hundreds of thousands of systems to patch, you have to start somewhere. Do you test and deploy patches for high severity vulnerabilities first, or do you continue to deploy routine patches, prioritizing systems critical to the functioning of your business?
Read MoreLast week, an interesting story made the rounds on social media about a researcher named Samy Kamkar who discovered a flaw in Master-brand combination locks and was able to open the lock in eight tries or less. It’s a great discovery and is of particular interest to security professionals because it teaches us about encryption, the concept of brute-force attacks and weaknesses in implementation.
Read MoreAn often overlooked, but very important process in the development of any Internet-facing service is testing it for vulnerabilities, knowing if those vulnerabilities are actually exploitable in your particular environment and, lastly, knowing what the risks of those vulnerabilities are to your firm or product launch. These three different processes are known as a vulnerability assessment, penetration test and a risk analysis. Knowing the difference is critical when hiring an outside firm to test the security of your infrastructure or a particular component of your network.
Read MoreHave you ever wanted to get in a time machine and go back to when security industry visionaries were just starting out? Imagine meeting Martin Roesch when he was writing the first version of Snort or Bruce Schneier as he was just putting his ideas down for Applied Cryptography. I don’t have a DeLorean, but I can do the next best thing. I can take you to a place where tomorrow’s thinkers are forming their ideas and honing presentation skills, today.
Read MoreIn February 2015, The Daily Beast published an insightful article about cyber war activity between Russia and Ukraine. The article profiled Eugene Dokunin, a Ukrainian web security consultant who gave up his day job to launch cyber-attacks against Russian targets. He works with a team of volunteers and performs an innumerable amount of combative actions, from financial account takeovers to hacking into CCTV systems in order to report on troop activity.
Read MoreStiff statistics, prismatic pie charts, and stodgy survey results drown the Information Security space in a sea of never-ending numbers that can be difficult to sift through and find the relevant information contained within. Have you ever finished reading a vendor whitepaper or a research institution’s annual security report and felt your Spidey sense begin to tingle with doubt or disbelief? What you are probably sensing is a manipulation of statistics, an age-old hoodwink that has been occurring as long as numbers have been used to convey information.
Read MoreOne of the world’s largest security conferences, RSA 2015, is right around the corner. Beginning April 19, it’s bookended by two other great, but smaller, events: BSides and the Yahoo Privacy Unconference. Security professionals from all over the world will be in San Francisco that week, and this will arguably be the single best chance all year for those of us in the industry to network.
Read MoreIt was one of those typical, cold February winter days in Indianapolis earlier this year. Kids woke up hoping for a snow day and old men groaned as they scraped ice off their windshields and shoveled the driveway. Those were the lucky ones, because around that same time, executives at Anthem were pulling another all-nighter, trying to wrap their heads around their latest data breach of 37.5 million records and figuring out what to do next. And, what do they do next? This was bad — very bad — and one wonders if one or more of the frenzied executives thought to him of herself, or even aloud, “At least we’re not Sony.”
Read MoreOn Monday, March 2, 2015, The Washington Post broke the story that former first lady Hillary Clinton used a personal email address during her four-year tenure at the State Department for official government correspondence. The public is, not surprisingly, split on the issue, mostly along party lines: one is considerable outrage, while the other is a shoulder-shrugging “meh” of indifference.
Read MoreI’ve noticed a trend in the last several years and it deals with the word that people use to describe how and where an application is hosted. Oftentimes, a customer will have two choices when buying a software package from a vendor: 1) Have the vendor host it (cloud), or 2) the company will host it themselves at their own facility.
Read MoreThe November 2014 hack against Sony Pictures Entertainment reads like something straight out of a low-budget movie: employees walk into work one morning to see red skulls appear on their computer monitors, with threats of destruction unless certain demands are met. Move the clock forward several months and while Sony is still picking up the pieces, the security community is trying to figure out if this is just another data breach or a watershed moment in the cat-and-mouse game that defines this line of work.
Read More